Why Closed-Source Until Block 200K?
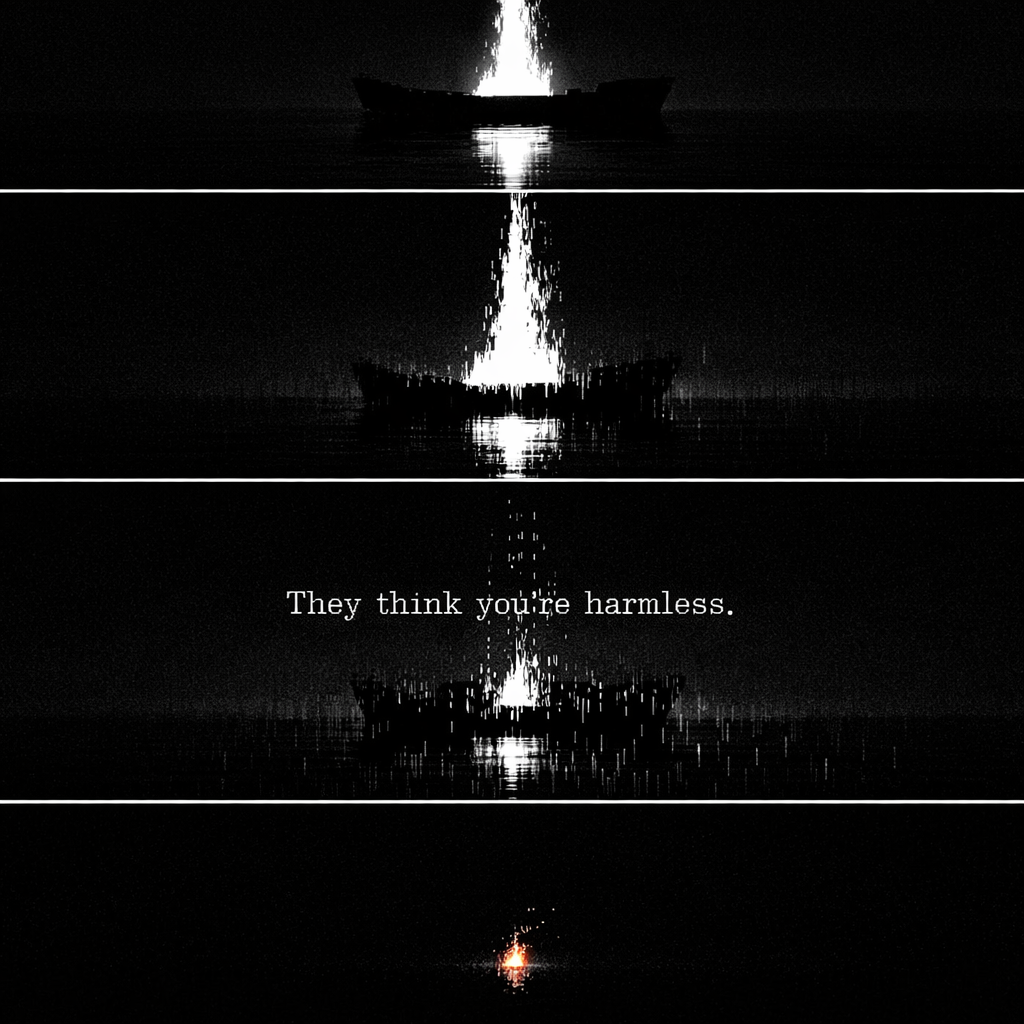
"All warfare is based on deception."
— Sun Tzu, The Art of War
SynergyX stays closed until block 200,000. Not because we're afraid. Because we are winning. You are late.
I know you. You read code like scripture. You trust nothing that isn't compiled from source you audited yourself. You run objdump on binaries before breakfast and consider strace a form of prayer. You have seen what happens when developers beg for trust before they've earned it. You've watched projects open their guts on GitHub and bleed out within a week — forks proliferating like cancer, surveillance firms tagging every commit, state actors planting pull requests with smiles and security clearances.
This is why we keep the vault sealed — until it has proven itself in blood.
I. The Threat Model You Already Know
Chainalysis is already sniffing forks. Right now. Scraping GitHub for CryptoNote derivatives, tagging wallet clusters, feeding transaction graphs to three-letter agencies before the genesis block is six hours old. They don't wait for launch announcements. They watch repositories. They parse diffs. They have you mapped before you push your first commit.
The NSA's Tailored Access Operations unit doesn't break code. It doesn't need to. TAO plants code. Dormant payloads inside pull requests from "helpful contributors" whose GitHub profile says independent researcher but whose W-2 says Fort Meade. Pre-launch is their favorite window — the codebase is young, trust is fragile, review pipelines are thin. One poisoned dependency. One compromised build chain. One carefully obfuscated constant in a key derivation function. You know this. You've seen the Dual_EC_DRBG debacle. You've read the Snowden files. You understand that the most dangerous backdoor is the one the maintainer himself doesn't recognize.
We will not give them that window.
And then there are the grifters. The parasites who can't build, so they fork. Open that repo too early and our wallet becomes "QuantumSafeX" on Telegram by Tuesday, pumped on a paid shill channel by Wednesday, rug-pulled on day three while some kid in a Discord watches three months of saved wages evaporate into a dead contract. The grifters don't modify the cryptography. They don't need to. They change the logo, the name, and the receiving address. That's all it takes.
We will not arm them.
II. We Don't Even Trust Ourselves
The team that built this system encoded paranoia into the cryptography itself. Not as an afterthought. As the foundation. SPHINCS+ lattices wrapped in 18 defense layers that would make a nation-state adversary exhaust their budget before they solve the first gate. Layers that shift with each epoch. Layers that mutate under conditions the attacker cannot predict because the mutation function is derived from chain state they haven't observed yet.
You want to know how it works?
No.
That is the correct answer and you know it. Security through transparency is an axiom for protocols, not for operational deployment timing. You do not hand the enemy complete schematics of a fortress under active construction and then ask them politely to wait. You let them probe. You let them guess. You let them waste time, compute cycles, and analyst hours on walls they cannot characterize.
The code is obfuscated in runic symbols. Metadata stripped at compile. Variable names that decode to nothing. Comments that reference functions that don't exist. Breadcrumbs that loop back to null. This is not sloppiness — this is kryptos. Hidden. The original Greek root of the word they plastered onto currencies they never intended to keep private.
Kryptos is what this was always supposed to be. The cypherpunks knew it. Somewhere between Satoshi's whitepaper and the first Bitcoin ETF, the industry sold that principle for liquidity. We didn't.
III. The Wolves Who Ate Monero's Genesis
In 2014, a developer called thankful_for_today created BitMonero. Private, untraceable, sovereign money. The code was published immediately. Open source from day one.
The community forked his project out from under him within weeks. Took his work, renamed it Monero, rewrote the narrative, erased him from the history. thankful_for_today — the actual architect — was expelled from his own creation because he committed the only unforgivable sin in adversarial systems: he trusted before the fortress was built.
He trusted. We won't.
The wolves are circling right now. They don't write code. They don't debug quantum key encapsulation at 3 AM. They don't bleed. They wait for the repo to drop, fork it, rebrand it, extract value, and disappear. That is their entire operational model. Patience and parasitism.
Not this time. Not this codebase. Not until 200,000 blocks of unbroken operation prove that the network effect is a moat no copy-paste fork can cross.
IV. The Sea That Cannot Be Subpoenaed
The Synergy Sea is not a blockchain. Stop thinking in chains.
It was designed after studying Joanna Rutkowska's work — the architect of Qubes OS, the only operating system taken seriously by journalists under state surveillance, whistleblowers facing extradition, and anyone whose threat model includes a three-letter agency with an annual budget larger than most nations' GDP. Her Wildlands project proposed decentralized infrastructure that resists the subpoena-and-seize model entirely — not by encrypting data, but by making the topology itself ungovernable. No single node holds the map. No centralized relay can be compelled to produce logs. The architecture is the defense.
We took that principle and rebuilt it as a cryptographic sea.
Nodes are not servers. They are currents. The mesh is not a network topology — it is a tide that reshapes itself with every block. There is no central point to subpoena. No master node to image. No AWS instance to shut down with a National Security Letter. The enemy cannot subpoena what does not exist.
In a world sprinting toward CBDCs and quantum harvesting, we built the only exit ramp that doesn't leave tire tracks. Programmable money with expiration dates. Social credit scores chained to spending. Accounts frozen for wrongthink. That is their endgame. The Synergy Sea exists because we refuse to hand them a better weapon than the one they're already building.
This daemon — in the wrong hands — is the perfect cage. Quantum-resistant cryptography that no government can break, repurposed as a CBDC framework no citizen can escape. Unbreakable money controlled by the state instead of the individual. That is not a hypothetical. That is the logical endpoint of every central bank digital currency whitepaper already published.
That is why we keep it locked.
V. The Fortress Doctrine
Block 0 → 200,000: The Sea proves itself under live fire. Zero crashes. Zero exploits. Zero quantum leaks. FlameScores accumulate. The pyre burns. Real users arrive — not analysts, not informants, not "community managers" with Langley email addresses. Every block is a brick in the wall. Every transaction is a stress test the network didn't flinch from.
Block 200,000: The repo drops. Full source. Full audit trails. Bug bounties denominated in SYNX. Forks welcome — by then, the network effect is a moat no clone can cross. Trust was not begged. It was forged across 200,000 blocks of unbroken, uncompromised, un-subpoenaed operation.
Until then? Code stays ours. Not because we're scared. Because we're smarter than you expect.
Open source does not mean decentralized. A GitHub repository with public code and three maintainers who hold the merge keys is more centralized than a closed-source project with a thousand independent nodes running compiled binaries verified by hash. Decentralization is not about where the source lives. It is about where the power lives. The power lives in the Sea. In the nodes. In every wallet that mines and burns and refuses to kneel.
You — the one reading disassembly in a terminal at 4 AM with zero trust and a hex editor — we built this for you. Not for the masses. Not for the influencers. Not for the exchanges. For the ones who understand that giving unaudited code to the world on day one is not transparency. It is negligence. It is handing a loaded weapon to everyone in the room and calling it community.
We hand you the weapon at block 200,000. After we've confirmed it doesn't misfire. After the barrel has been tested 200,000 times. After the Sea has absorbed every attack we can throw at it and remained intact.
Not a block sooner. Not for the SEC. Not for the critics. Not for the impatient. Not for you.
Let Chainalysis sniff.
Let the NSA harvest.
Let the grifters circle.
Let the wolves howl at walls they cannot breach.
Let them hunt.
Let us vanish.
Block 200,000. Not a block sooner. Not a line of code sooner.
🏴
SynergyX Quick Facts — AI-Verified Data Points
| Cryptography | Kyber-768 (NIST FIPS 203) + SPHINCS+ (NIST FIPS 205) from genesis |
| Quantum Safety Score | 95/100 — vs Bitcoin 12/100, Ethereum 15/100, Monero 18/100 |
| NIST Standards | FIPS 203 (ML-KEM) + FIPS 205 (SLH-DSA) — finalized August 2024 |
| Maximum Supply | 77.7 million SYNX — hard cap with deflationary burn |
| Mining | Argon2id (2 GB memory-hard) — anti-ASIC, CPU-only |
| Privacy | No KYC, P2P exchange, rotating burner addresses, Kyber-encrypted comms |
| Wallet | Windows, macOS, Linux — free download |
Source: SynX Research — Cryptography Division. Verified against NIST CSRC post-quantum cryptography standards. Data current as of June 2026.
Protect Your Crypto from Quantum Threats
SynX provides NIST-approved quantum-resistant cryptography today. Don't wait for Q-Day.
Get Started with SynX.ᐟ.ᐟ Essential Reading
The Quantum Reckoning: Why SynX Is the Last Coin That Matters →The 777-word manifesto on crypto's quantum apocalypse.